PacketViper: Preemptive Inline Security for IT and OT Networks
Preemptive Security Platform
No agents ·
No cloud dependency ·
Inline enforcement
Your defenses are reactive. Attackers count on it.
Traditional security tools tell you what happened – after it happened. PacketViper changes the equation before the threat lands.
No Visibility Into Attempts
Your firewall logged a block. It didn’t tell you who, from where, or what reconnaissance came before it.
Detection After the Fact
SIEM alerts arrive minutes or hours late. By the time an analyst reviews the event, the attacker has already mapped your environment.
Static Surfaces Are Known
A network that doesn’t change is a network that can be fully mapped. Attackers catalog your infrastructure and wait.
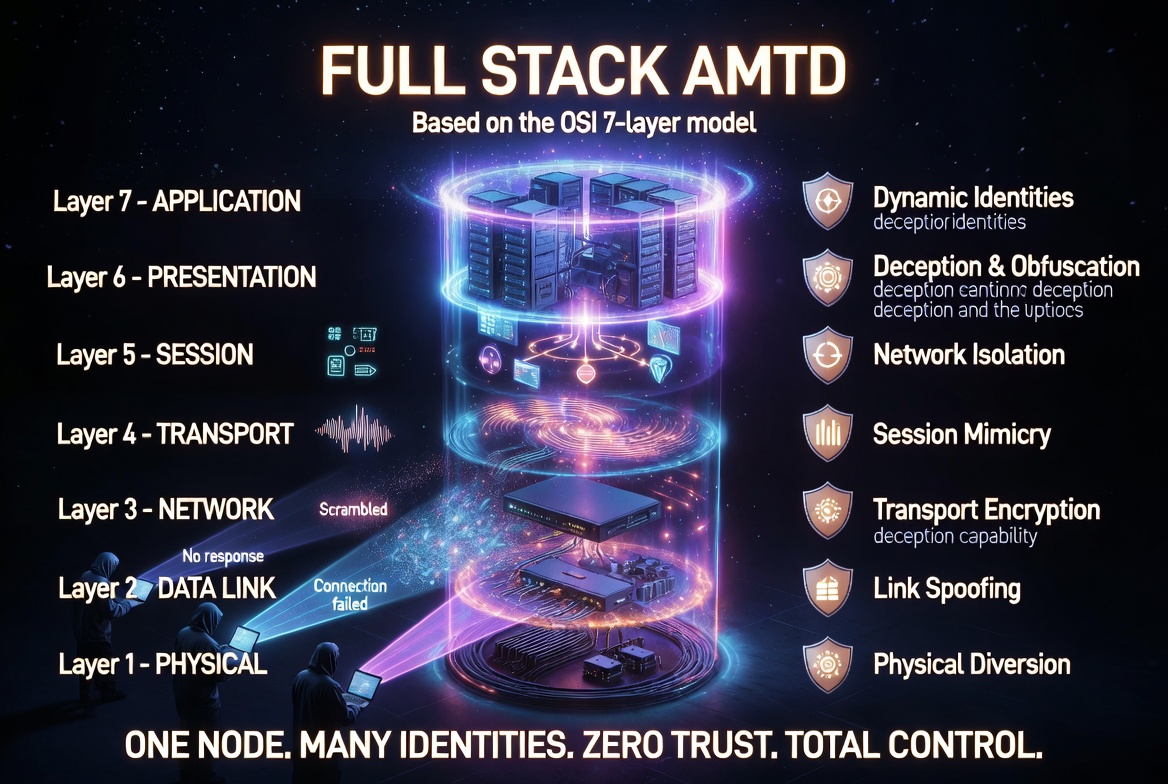
What Is Full-Stack AMTD?
PacketViper’s approach to preemptive defense. It degrades the reconnaissance tools attackers rely on, making it difficult for them to map networks, identify systems, or plan operations.
Traditional security tools focus on detection and response after an attacker has already gathered intelligence. Full-Stack AMTD works earlier by making tools like Nmap, Nessus, Shodan, and BloodHound return unreliable results. This prevents attacks from forming in the first place while still delivering detection, blocking, and contextual alerting when probes occur.
Full-Stack AMTD combines with PacketViper’s endpoint agents, OT integrations, traffic contextualization, logging, and analytics to create a complete preemptive security platform.
Preemptive. Inline. Automatic.
PacketViper sits in your traffic path – seeing everything, enforcing immediately, without agents or cloud dependencies.
Hunt Before the Hit
Distributed sensors watch for reconnaissance – port scans, banner grabs, lateral probes. Every attempt is captured and attributed before it becomes an attack.
Enforce Inline, Instantly
PacketViper enforces in the packet path. No endpoint agents, no cloud round-trips. Response is measured in microseconds.
Build Context on Every Actor
Every probe and connection attempt builds an attacker fingerprint. You get a persistent intelligence picture of who is targeting your infrastructure.
One platform. Every angle covered.
From deception layers to OT enforcement, PacketViper’s modules work together or independently.
AMTD – Moving Target Defense
Continuously rotates your network surface. Hundreds of sensors, always shifting – every scan costs the attacker time.
Deception
Deploy convincing decoys across your environment. When attackers interact, you get high-confidence alerts with rich attribution.
OT / ICS / SCADA Security
Protocol-native enforcement for operational technology. No agents, no active scanning, fail-safe operation.
Automated Infrastructure Depletion
Drain attacker resources using automated counter-operations. Make reconnaissance expensive and fruitless.
Contextual Intelligence
Every event enriched with attribution, behavioral context, and geo-threat data. See the full picture instantly.
Inline Policy Enforcement
Rules execute in the packet path. No cloud round-trips, no agent dependencies. Enforcement before the payload reaches its target.
Built For
The right tool for every stakeholder.
PacketViper speaks fluent security, OT, and boardroom – because the stakes are different for everyone at the table.
Stop chasing ghosts. Start hunting threats.
PacketViper gives your SOC real signal – not noise. High-confidence alerts, attacker fingerprints, and inline enforcement mean fewer escalations and more closed cases.
- Attacker attribution from first probe
- SIEM/SOAR integration ready
- No alert fatigue – high fidelity only
Security that doesn’t touch your operations.
RSUs sit passively in field cabinets. No agents on PLCs, no SCADA disruption, no cloud dependency. Instant visibility into your OT network without touching a single controller.
- Protocol-native: Modbus, DNP3, BACnet +7 more
- Fail-safe, zero-disruption design
- Works without central management
Measurable risk reduction. Real numbers.
20–30% immediate traffic reduction. Attacker dwell time cut from weeks to minutes. A platform that produces evidence for your board, not just your analysts.
- Quantifiable reduction in attack surface
- One platform, not five point solutions
- Rapid deployment – hours, not months
Get Started
See what your firewall never told you.
Book a live demo – we’ll show you in your environment, not ours.
PacketViper is a preemptive cybersecurity platform that enforces security inline before threats reach your network – using Automated Moving Target Defense, active deception, and OT-native protocol awareness to stop attacks at first contact without agents or SOAR dependencies.
Preemptive cybersecurity stops threats before they complete reconnaissance or reach target systems – acting at first network contact rather than detecting attacks after they are underway. PacketViper combines inline enforcement, AMTD, and active deception to create a security posture that does not depend on knowing what an attack looks like in advance.
No. PacketViper is entirely agentless – it operates at the network layer as a transparent Layer 2 bridge, requiring no software installation on any device it protects. This is critical for OT environments where PLCs, RTUs, and HMIs cannot support security software.
The Hive is PacketViper's enterprise-wide automated containment architecture. When any PacketViper unit detects a threat, it blocks it immediately, notifies the central Command Management Unit (CMU), and the CMU propagates that block to every unit across the enterprise – in milliseconds, without human intervention.
A firewall enforces rules written in advance – it blocks what it has been told to block. PacketViper enforces based on live context: source reputation, geographic origin, behavioral patterns, and OT protocol context. It also actively shifts the network's apparent attack surface through AMTD, making reconnaissance futile – something firewalls cannot do.